$ cat /etc/profile.d/liam.sh
NAME="Liam Romanis"
ROLE="Senior Penetration Tester | Principal Security Consultant | Freelance"
EXPERIENCE="29+ years in offensive security"
FORMER_ROLE="CESG CHECK Team Leader (1999–2023) — one of the longest continuous tenures in the scheme"
SECTORS="UK Government · MOD · Defence Primes · Financial Services · Telecomms · CNI · Commercial"
FOCUS="Manual testing excellence · Vulnerability research · Pragmatic risk-based assessment"
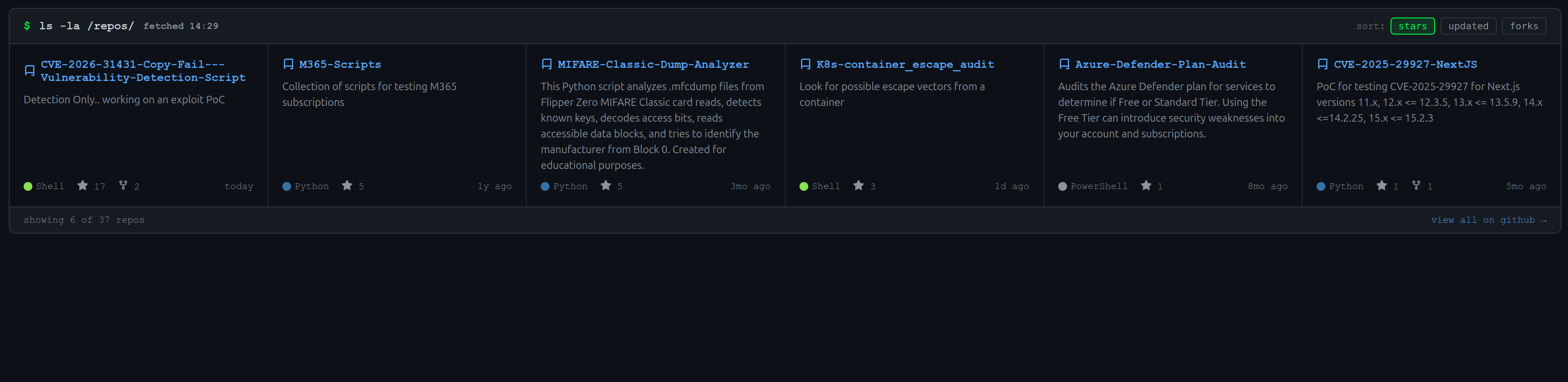
CURRENTLY="Freelance pentest engagements + AI Red Teaming courses"Python 3 tool to analyze AWS IAM policies for risky permissions. Tracks affected principals, simulates sensitive actions, detects privilege escalation patterns, and flags cross-account trust exposures. Outputs findings in Table, JSON, or CSV with severity scoring (0–100).
Python · AWS · IAM · PrivEsc Detection · Cloud Security
🦑 Snecky
Passive network sniffing tool that simplifies detection and reporting of network protocols with weak configurations. Outputs results in Nessus-compatible format for seamless import into reporting tools.
Python · Network Security · Passive Recon · Nessus Integration
Proof-of-Concept for CVE-2025-29927 — a critical middleware bypass vulnerability affecting Next.js versions 11.x through 15.x. For authorised security testing and verification.
Python · CVE Research · Next.js · Web App Security
| Tool | Description |
|---|---|
| SNMPPLUX | SNMP enumeration and analysis tooling |
| LibScanner | Library/dependency scanning utility |
| ORR | Offline reporting and review tool |
| SSLScanner (PHP) | SSL/TLS configuration scanner |
| Azure MFA Auditor | Identifies Azure users without MFA where standard tooling fails |
| Azure Conditional Access Extractor | Extracts and analyses Conditional Access policies, outputs CSV artefacts |
| Azure Storage Assessor | Internal and external Azure storage enumeration and assessment |
✔ UK Government & MOD ✔ Defence Primes
✔ Financial Services (MetroBank, ICAP, EBLF) ✔ Telecommunications
✔ Critical National Infrastructure ✔ NHS & Central Government
✔ Commercial Enterprise ✔ SaaS & Cloud Platforms
Click me:
┌──────────────────────────────────────────────────────────────────────────────┐
│ "Security is not a product, but a process — and I've been in that │
│ process longer than most frameworks have existed." │
└──────────────────────────────────────────────────────────────────────────────┘
All tools and PoCs published here are intended for authorised security testing and research only.






















































-gold?style=flat-square&color=FFD700)